Azure VM Confugruation
- OS: Ubuntu Server 17, etc
- Virtual Network/Subnet: 10.0.0.0/24
- Private IP: 10.0.0.4
- Public IP: 51.x.x.x
- Inbound security rules
- Allow UDP 500
- Allow UDP 4500
Enable IP forwarding
Install StrongSwan
sudo apt-get install strongswan
Config IPSec – /etc/ipsec.conf
# ipsec.conf - strongSwan IPsec configuration file
# basic configuration
config setup
# strictcrlpolicy=yes
# uniqueids = no
conn %default
ikelifetime=60m
keylife=20m
rekeymargin=3m
keyingtries=1
authby=secret
keyexchange=ikev2
conn 41D
auto=add
type=tunnel
aggressive=no
ike=aes256-sha1-modp1024,3des-sha1-modp1024
esp=aes256-sha1,3des-sha1
mark_in=42
mark_out=42
left=10.0.0.4
leftsubnet=0.0.0.0/0
leftid=51.x.x.x
leftauth=psk
leftfirewall=yes
right=59.x.x.x
rightsubnet=192.168.5.0/24
rightauth=psk
rightfirewall=yes
Config IPSec – /etc/ipsec.secrets
# /etc/ipsec.secrets - strongSwan IPsec secrets file
59.x.x.x 51.x.x.x : PSK "secret"
Config IPSec – /etc/strongswan.conf
# strongswan.conf - strongSwan configuration file
#
# Refer to the strongswan.conf(5) manpage for details
#
# Configuration changes should be made in the included files
charon {
install_routes=no
install_virtual_ip=no
load_modular = yes
plugins {
include strongswan.d/charon/*.conf
}
}
include strongswan.d/*.conf
Config IPSec – Reconnect
ipsec restart
ipsec statusall
Config VTI
ip tunnel add vti0 local 10.0.0.4 remote 59.x.x.x mode vti key 42
ip link set vti0 up
Config Routing
ip route add 192.168.5.0/24 dev vti0
Config SNAT and DNS Forwarding
iptables -t nat -A PREROUTING -p udp --dport 53 -j DNAT --to 8.8.8.8
iptables -t nat -A PREROUTING -p tcp --dport 53 -j DNAT --to 8.8.8.8
iptables -t nat -A POSTROUTING -s 192.168.5.0/24 -o eth0 -j SNAT --to-source 10.0.0.4
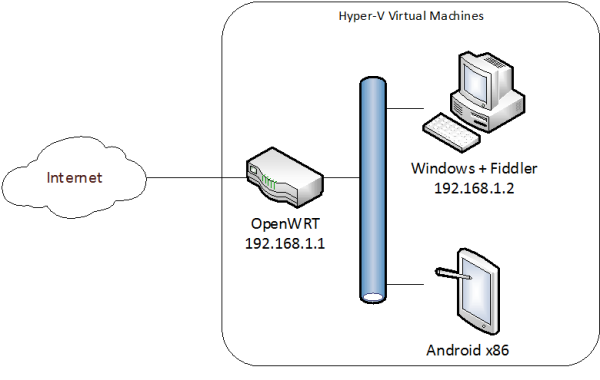
OpenWRT/LEDE Configuration
Install StrongSwan and VTI packages
strongswan-minimal
ip-full
kmod-ip-vti
vtiv4
Config IPSec – /etc/ipsec.conf
# ipsec.conf - strongSwan IPsec configuration file
# basic configuration
config setup
# strictcrlpolicy=yes
# uniqueids = no
conn %default
ikelifetime=60m
keylife=20m
rekeymargin=3m
keyingtries=1
authby=secret
keyexchange=ikev2
conn UKGW
auto=start
closeaction=restart
type=tunnel
aggressive=no
ike=aes256-sha1-modp1024,3des-sha1-modp1024
esp=aes256-sha1,3des-sha1
mark_in=42
mark_out=42
left=59.x.x.x
leftsubnet=192.168.3.0/24
leftid=59.x.x.x
leftauth=psk
leftfirewall=yes
right=51.x.x.x
rightsubnet=0.0.0.0/0
rightid=51.x.x.x
rightauth=psk
rightfirewall=yes
Config IPSec – /etc/ipsec.secrets
# /etc/ipsec.secrets - strongSwan IPsec secrets file
59.x.x.x 51.x.x.x : PSK "secret"
Config IPSec – /etc/strongswan.conf
# strongswan.conf - strongSwan configuration file
#
# Refer to the strongswan.conf(5) manpage for details
#
# Configuration changes should be made in the included files
charon {
install_routes=no
install_virtual_ip=no
load_modular = yes
plugins {
include strongswan.d/charon/*.conf
}
}
include strongswan.d/*.conf
Config IPSec – Reconnect
ipsec restart
ipsec statusall
Config VTI
ip tunnel add vti0 local 59.x.x.x remote 51.x.x.x mode vti key 42
ip link set vti0 up
Config Routing 1
ip route add 10.0.0.0/24 dev vti0
Config Routing 2 – set subnet default route to Azure VM
ip rule add from 192.168.3.0/24 table 1000
ip route add 0.0.0.0/0 dev vti0 table 1000
ip route show table 1000
iptables -A PREROUTING -p udp -s 192.168.3.0 --dport 53 -j DNAT --to 10.0.0.4
iptables -A PREROUTING -p tcp -s 192.168.3.0 --dport 53 -j DNAT --to 10.0.0.4
Others
- Add interface and zone for vti0. Allow transfer to/from LAN.
- Enable MSS Clamping for VTI interface.